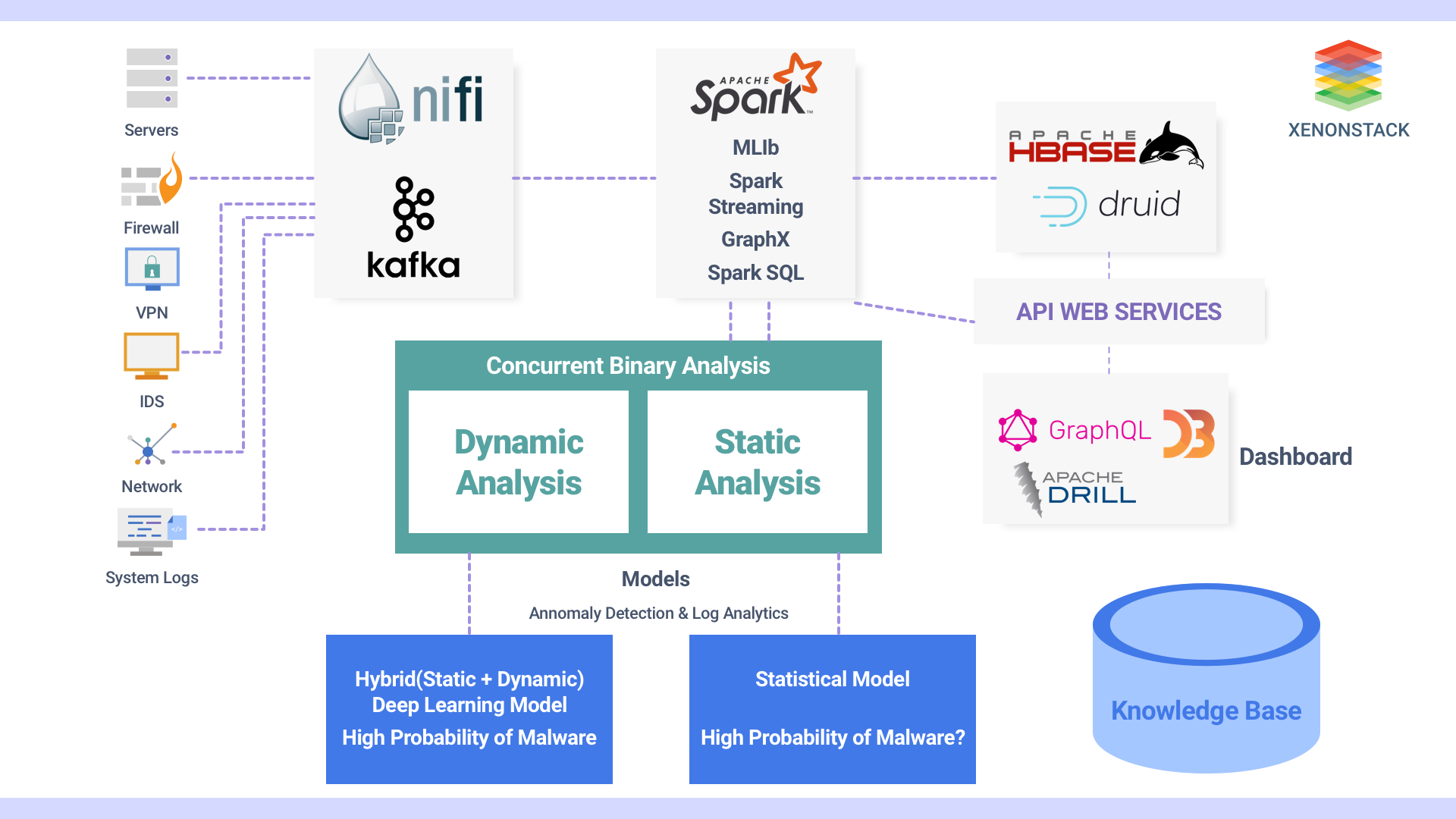
Network Security Monitoring and Analytics
Working on cybersecurity and threat intelligence, there are so many points to focus. We have to be careful so that there shouldn’t be any loopholes in intelligence which can eventually result in losing confidential information. Building network security monitoring and analytics solution was challenging. But it helps to address different network security concern and played an important role to overcome security threats. We focused on the following points while making our platform.
-
Feature Engineering
-
Proactive steps on Correlation and Anomaly Detection
-
Threat Intelligence
-
Automated Learning
Architecture Diagram

Thanks for submitting the form.