Overview of Advanced Threat Analytics and Intelligence
The security aspect has changed dramatically over recent years. Cyberattacks nowadays have become more pervasive, persistent, and proficient than ever at escaping and contaminating traditional security architecture. Cyber threats have become more complex and complicated. Many companies face stealthy attacks on their systems. These attacks target intellectual property, consumer information theft, or the encryption of essential data for ransom.
Therefore, you must know what is coming to protect your IT assets, secure your digital interactions, detect and manage inevitable breaches, and safeguard your business chain and regulatory compliance. Threat Detection is the art of identifying attacks on a computer. While there is a large variety of Cyber Security attacks, most of them fit into one of four categories -
- Probe
- Denial of Service (Dos)
- User to Root
- Remote to User
Hence, companies are looking for cybersecurity services and Solutions to ensure the security of their IT network. In this use case, we will guide you through how we built an effective cybersecurity and threat detection system using machine learning.
Apache Metron Overview
Apache Metron is a cybersecurity application framework that allows organisations to rapidly detect cyber anomalies by ingesting, processing, and storing various security data feeds at a scale level.
Apache Spot Architecture for Cyber Security
Apache Spot is a cybersecurity project that aims to bring Advanced Analytics to all IT Telemetry data on an open, scalable platform. It expedites threat detection, investigation, and remediation via machine learning and consolidates all enterprise security data into a comprehensive IT telemetry hub based on open data models.
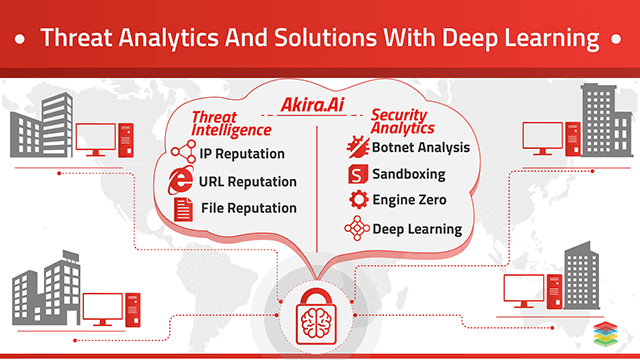
Threat Detection Using Deep Learning
A multi-layered Deep learning-based system is very robust, scalable, and adaptable. A risk score denotes all the identified incidents and patterns to help investigate the breach, control data loss, and take precautionary actions for the future.
Threat Detection Using Machine Learning
A Machine learning-based Threat Detection system automates extracting insights from file samples by better generalising the identification of unknown variations. It also helps reduce human analysis time.
Challenges to Real-Time Cyber Threat Intelligence
-
To perform Real-Time Threat Intelligence on trillions of messages per year.
-
Storing and processing the unstructured security data.
-
Combine Machine Learning and Predictive Analytics to perform Real-Time Threat Analytics.
Solution Offerings for Threat Detection and Cyber Security
Threat Analytics and Intelligence by automating the process of Threat Detection and Analysis. The following steps are performed to Automate the process -
-
Network Dataset
-
Pre-Processing of Data
-
Feature Extraction
-
Reduce Data Amount
-
Improve Accuracy
-
Avoid Overfitting
Training and Testing of Data Using Classification Models
-
Decision Tree
-
Random Forest
-
Naive Bayes
-
KNN
-
Result Analysis
Enabling Cyber Security with Apache Metron and Spot
Apache Metron is a cybersecurity application that enables streaming data security, detection, and response to threats. It provides security monitoring and analysis, which has a mechanism to store, capture, and normalise any security telemetry at excessively high rates. Enables real-time processing, advanced behavioural analytics, and enrichment application—efficient information storage for concise security visibility. Moreover, a centralised view of data and alerts is passed through the system. It comprises four key capabilities -
-
Security Data Lake provides a mechanism to search and query for Operational Analytics—cost-effective storage of enriched telematic data.
-
Pluggable Framework will be used to add new enrichment services to raw streaming data. Pluggable Extensions for threat feeds and the ability to customise security dashboards.
-
Security applications include alerting, replay utilities, evidence storage, and agents to ingest data sources.
-
Threat Intelligence Platform includes defence techniques using Anomaly detection and Machine Learning algorithms applied in Real-Time events.
Apache Spot for Cyber Security and Threat Intelligence Solutions
Apache Spot is a cybersecurity project that leverages packet and flow analysis insights involving threat detection, investigation, advanced analytics, and identifying unknown threats, perimeter flows, internal flows, and DNS flows to create fast and efficient data analysis. It uses the Parallel Ingest Framework, Machine Learning and Operational Analytics to detect -
-
Suspicious DNS Packets
-
Reduction of Mean Time to Incident Detection & Resolution (MTTR)
-
Threat Incident and Response
-
Threat Hunting
-
Open Data Models
-
Detection of Known and Unknown Threats via Machine Learning
Next Steps with Threat Analytics
Talk to our experts about implementing compound AI system, How Industries and different departments use Agentic Workflows and Decision Intelligence to Become Decision Centric. Utilizes AI to automate and optimize IT support and operations, improving efficiency and responsiveness.
.webp?width=1921&height=622&name=usecase-banner%20(1).webp)