What is Istio?
Istio is an open-source tool written in Go that helps create an abstraction layer above various Microservices running in Kubernetes. Although it is also available for other platforms, it’s battle-tested in production on Kubernetes. It’s installed using manifest yaml files and Helm Chart, which bootstraps all Istio components on the cluster. It adds a layer of transparency between distributed applications.
It has its APIs to integrate with other open-source logging or telemetry tools, such as Prometheus and Grafana.
A Service Mesh provides dedicated infrastructure layer atom application. Click to explore about, Service Mesh Architecture
Why Istio is essential?
Although there are several other Service Mesh tools, such as Linkerd, Istio is stable, has more features, and provides more granular security. It also helps trace all calls, requests, and responses to whole paths. It helps in tracing the Root Cause Analysis of issues. It helps to -
-
Connect Microservices.
-
Control various API calls between services & traffic flow between them.
-
Secure Microservices.
-
Provides security by default - No modifications required in app code & infrastructure.
-
Ultra Defense: Provides multiple layers of security by integrating with another security system.
-
Allow traffic encryption, which helps against MITM attacks.
-
Control Microservices.
-
Applies enforcement policies.
-
Observe services Microservices.
-
Provide Auto-tracing, logging, and monitoring of all Microservices to visualize what's happening under the hood.
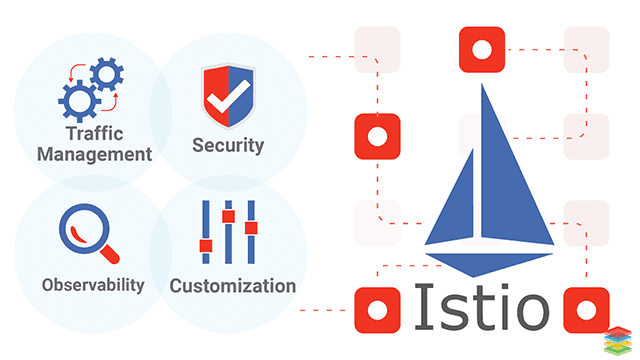
What are the features of Istio?
-
Traffic management - All traffic is managed through Istio side-cars, deployed in parallel to the service.
-
Security—Istio moves security from the application layer to the network layer. Developers focus on domain logic only. It manages all security mechanisms using its components.
-
Observability—Istio provides Tracing, Log management, and Monitoring through patterns depicting failures. The performance of requests and responses upstream and downstream is determined. Load testing is done on services to see performance bottlenecks.
-
Support for platforms—Istio is available for Kubernetes, Nomad, Mesos, and more. It is testing in production on Kubernetes.
-
Customization and Integration - Policies enforced, customized, and integrated with ACLs, logging, and monitoring solutions.
Envoy is most comparable to software load balancers such as NGINX and HAProxy, but it has many advantages than typical proxies. Click to explore about, Envoy Proxy Working Architecture
What is the architecture of Istio?
The service mesh is divided into a data plane and a control plane. The data plane consists of an intelligent proxy (Envoy) deployed as sidecars parallel to app containers. These proxies control all network communication between Microservices.
The mixer is used as a policy and telemetry central hub. The control plane deploys and configures proxies to route inbound and outbound traffic. The control plane configures Mixers to enforce policies on apps and collect telemetry information to be sent to monitoring systems.
How Istio works?
A Service Mesh provides a collection of lightweight proxies alongside containers in a Kubernetes pod. Each proxy acts as a gateway to interactions that occur between containers. The proxy forwards the request to load across the Service Mesh to the appropriate downstream service containers that serve the request. The controller in the control plane orchestrates the connections between proxies.
The control plane knows about each request/response, even though the service/application traffic flows directly between proxies. The controller provides access control policies and collects metrics from containers for telemetry and observation. The controller tightly integrates with Kubernetes, an open-source system for automating the deployment and orchestration of containerized applications. Let's understand the significant components of Istio -
Guide to Using Envoy
Istio uses Envoy proxy for --
Load balancing
-
Fault injection
-
Service Discovery
-
Health checks
-
Envoy was deployed as a sidecar parallel to the container.
Pilot Applications
-
Enables dynamic service discovery for sidecars.
-
Manages traffic for routing.
-
Provide resiliency.
-
The pilot converts the routing rule to sidecars at runtime.
-
Every application has its service proxy. Application instances access their service proxy.
Galley Properties
-
Provides top-level API configuration.
-
It processes and distributes various components of Istio.
Citadel Overview
Citadel provides app service-to-service and authentication for end users with built-in Identity and User Credential Management.Istio Deployment on Kubernetes
It is available as Kubernetes manifest files or Helm chart used to deploy it. All components are deployed in a namespace `istio-system`. Grafana deployed along with the stack to visualize various metrics. Grafana uses Prometheus as backend.curl -L https://git.io/getLatestIstio | sh -
cd istio-1.0.3
- Installation .yaml files for Kubernetes in install/
- Sample applications in samples/
- The distinct client binary is in the bin/ directory.
export PATH=$PWD/bin:$PATH
kubectl apply -f install/kubernetes/helm/helm-service-account.yaml
helm init --service-account tiller
kubectl delete -f install/kubernetes/helm/istio/templates/crds.yaml -n istio-system
Sidecar installation
Each pod in the mesh must run an Istio sidecar using Envoy. The following sections describe ways of injecting sidecar inside a pod - manually using the istioctl CLI tool or automatically using the Istio sidecar injector.Manual sidecar injection
kubectl apply -f <(istioctl kube-inject -f ./samples/sleep/sleep.yaml)
kubectl get configmap istio-sidecar-injector -o=jsonpath='{.data.config}' -n istio-system > inject-config.yaml
kubectl get configmap istio -o=jsonpath='{.data.mesh}'-n istio-system > mesh-config.yaml
istioctl kube-inject \
--injectConfigFile inject-config.yaml \
--meshConfigFile mesh-config.yaml \
--filename samples/sleep/sleep.yaml \
--output sleep-injected.yaml
kubectl apply -f sleep-injected.yaml
Automatic sidecar injection
kubectl api-versions | grep admissionregistration
helm template --namespace=istio-system --set sidecarInjectorWebhook.enabled=false install/kubernetes/helm/istio > istio.yaml
kubectl create ns istio-system
kubectl apply -n istio-system -f istio.yaml
kubectl apply -f samples/sleep/sleep.yaml
kubectl get deployment -o wide
kubectl get pod
kubectl label namespace default istio-injection=enabled
kubectl get namespace -L istio-injection
kubectl delete pod sleep-776b7bcdcd-7hpnk
kubectl get pod
kubectl describe pod sleep-776b7bcdcd-bhn9m
kubectl label namespace default istio-injection-
kubectl delete pod sleep-776b7bcdcd-bhn9m
kubectl get pod
Running demo app - Bookinfo Application
kubectl apply -f <(istioctl kube-inject -f samples/bookinfo/platform/kube/bookinfo.yaml)
kubectl label namespace default istio-injection=enabled
kubectl apply -f samples/bookinfo/platform/kube/bookinfo.yaml
kubectl get services
kubectl get pods
kubectl apply -f samples/bookinfo/networking/bookinfo-gateway.yaml
kubectl get gateway
export GATEWAY_URL=$INGRESS_HOST:$INGRESS_PORT
Confirm application running
curl -o /dev/null -s -w "%{http_code}\n" http://${GATEWAY_URL}/productpage
What are the best practices for Istio?
Enable a service layer adds an extra abstraction layer over existing infrastructure, follows some best practices so that it doesn't create overhead, and reaps its benefits instead of dealing with its complexity. Use only when Microservices more than 15 or so, otherwise, for less number of services will add operational complexity. Always try to inject sidecars automatically instead of manually, as in this way, the CI/CD pipeline runs efficiently without affecting deployment downtime.
Use Dynamic request routing for shifting traffic in modern deployment use cases such as blue-green deploys, Canary, A/B testing, etc. It will help make the transition smooth in real-time. Customize Grafana dashboards to gain more insight into the Microservices communication. Add horizontal pod auto-scaler for all deployments in the cluster. Try to leverage most of the features of Istio, but use only one feature at a time, as it might get complicated if you try to use all features simultaneously.
What are the benefits of Istio?
Istio has a lot of benefits for modern Cloud Native applications. Practical benefits discussed above, the benefits listed below are mainly on the business side of technology --
Provides a transparent communication layer between independent applications running inside the cluster.
-
It allows management of all Micro-services as and when they grow in several sizes.
-
Istio provides Traffic Management between all Microservices.
-
Istio Abstracts the layer of reliably delivering requests between services through a proxy.
-
Istio increases the performance and reliability of infrastructure.
-
Istio’s Traffic Management decouples traffic flow and scaling of infrastructure.
-
Extract telemetry data from proxy containers and send them to a monitoring dashboard.
-
Istio is capable of handling ambiguous network failures and allowing self-healing infrastructure.
Tools for Enabling Service Mesh on Istio
The following tools come under the umbrella of Istio and help in the successful creation of a Service Mesh: Istio itself, deployed cluster-wide in its own namespace. istioctl is a Command-Line utility to manage Istio resources inside the cluster. Istio can be deployed in the Kubernetes Platform Setup. Ex - kops cluster running on AWS.Nomad & Consul.

- Explore here about Microservices for Java and Golang
- Read more about Data Mesh and its Benefits
Next Steps with Istio Service Mesh Architecture
Talk to our experts about implementing compound AI system, How Industries and different departments use Agentic Workflows and Decision Intelligence to Become Decision Centric. Utilizes AI to automate and optimize IT support and operations, improving efficiency and responsiveness.
.webp?width=1921&height=622&name=usecase-banner%20(1).webp)


