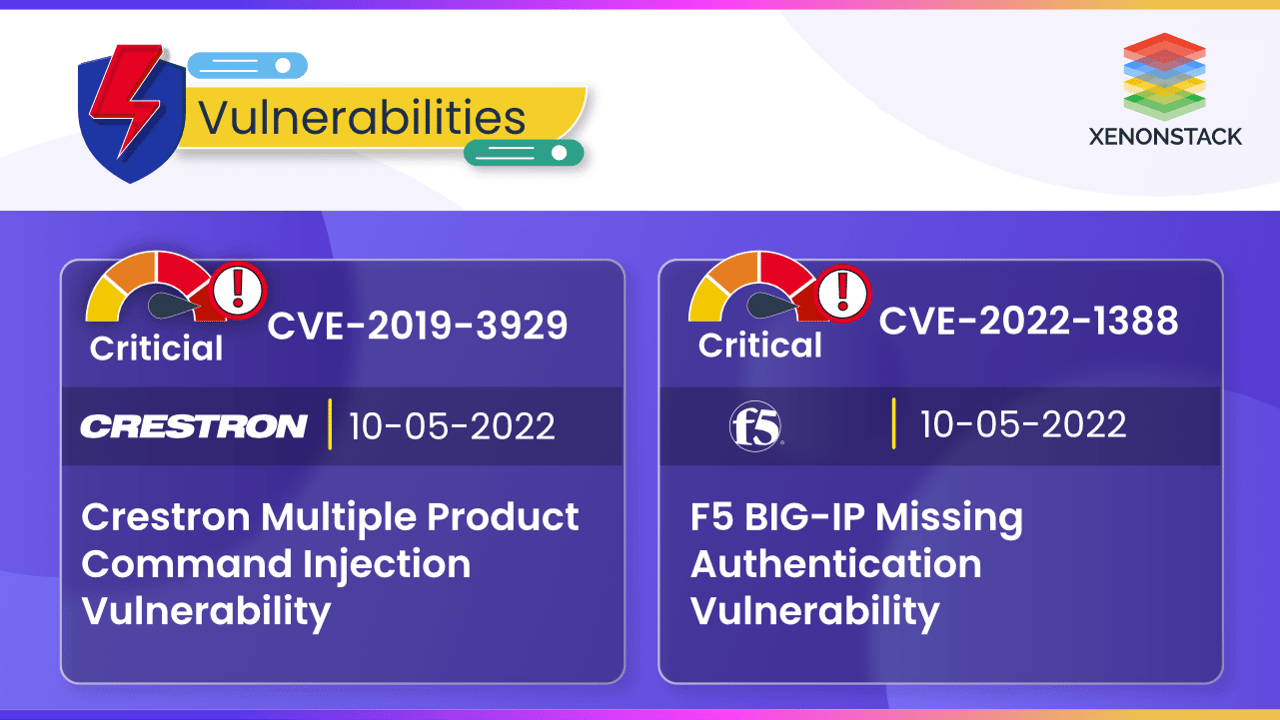
What is CVE-2019-3929?
(Crestron Multiple Products Command Injection Vulnerability)
A vulnerability was discovered in Creston AM-100 and AM-101. This vulnerability affects the file file_transfer.cgi of the component called HTTP Endpoint. The exploitation of this vulnerability can lead to privilege escalation. Exploitation can be done with any authentication.
Impact of CVE-2019-3929:
The following versions are affected by the vulnerability:
- Crestron AM-100 1.6.0.2
- Crestron AM-101 2.7.0.1
- Barco wePresent WiPG-1000P 2.3.0.10
- Barco wePresent WiPG-1600W 2.4.1
- Extron ShareLink 200/Extron ShareLink 200 250 2.0.3.4
- Teq AV IT WIPS710 1.1.0.7
- SHARP PN-L703WA 1.4.2.3
- Optoma WPS-Pro 1.0.0.5
- Blackbox HD WPS 1.0.0.5
- InFocus LiteShow3 1.0.16
- InFocus LiteShow4 2.0.0.7
| CVE ID | CVE-2019-3929 |
| Vulnerability Name | Crestron multiple Product command Injection vulnerability |
| Vendor | Crestron |
| Product | Multiple Products |
| Description | A vulnerability was discovered in Creston AM-100 and AM-101. This vulnerability affects the file file_transfer.cgi of the component called HTTP Endpoint. The exploitation of this vulnerability can lead to privilege escalation. Exploitation can be done with any authentication. |
| Date added to the catalog | 2022-05-10 |
| Severity (scale of 10) | 9.8 (Critical) |
| Remediation | It is possible to mitigate the vulnerability through a firewall. |
What is CVE-2022-1388?
(F5 BIG-IP Missing Authentication Vulnerability)
CVE-2022-1388 is a remote code execution vulnerability in iControlREST of the BIG-IP product. Attackers can exploit this vulnerability by bypassing F5’s iControl Rest authentication and running arbitrary code. This is a critical vulnerability. A combination of hardware and software F5 BIG-IP allows for inspection and encryption of traffic that is passing through a network. It works as a load balancer, full proxy, and application firewall. F5 BIG-IP is widely used and is one of the commonly exploited services.
| CVE ID | CVE-2022-1388 |
| Vulnerability Name | F5 BIG-IP Missing Authentication Vulnerability |
| Vendor | F5 |
| Product | BIG-IP |
| Description | F5’s BIG-IP consists of a missing authentication in critical function vulnerability that can allow a remote code execution which can lead to the creation or deletion of files, or disabling of services. |
| Date added to the catalog | 2022-05-10 |
| Severity (scale of 10) | 9.8 (Critical) |
| Impact | This vulnerability impacted the version from 16.1.0 to 16.1.2, 15.1.0 to 15.1.5, 14.1.0 to 14.1.4, 13.1.0 to 13.1.4 , 12.1.0 to 12.1.6, 11.6.1 to 11.6.5. |
| Remediation | It is recommended to update the F5 BIG-IP deployments to one of the versions mentioned below: 17.0.0 16.1.2.2 15.1.5.1 14.1.14.6 13.1.5 |
Conclusion
Crestron CVE-2019-3929 and F5 CVE-2022-1388 vulnerabilities can exploit the authentication, and arbitrary code leads to privilege escalation. Metasecure actively monitors these latest vulnerabilities and ensures complete coverage for our clients.
Click here to explore more Latest Vulnerabilities and their Remediations
.webp?width=1921&height=622&name=usecase-banner%20(1).webp)


