
Introducing Google Security Services
Data Security is a primary design consideration for all of Google's infrastructure, products, and personnel operations. The collaboration of Google with the security research community enables them to address vulnerabilities quickly or prevent them entirely. Google Security Services is indeed required to secure GCP and other google services.Private Service Connect will enable easy, secure access to Google’s own Cloud services, 3rd party services, and in-house enterprise applications. Source: ForbesOrganizations have typically turned to the public cloud for cost reductions or increased private data centers' ability. However, organizations are now looking for security primarily at the public cloud, realizing that Cloud Service providers deliver secure infrastructure. It was thus helping them invest more in people and processes.
Google Infrastructure Security Layers
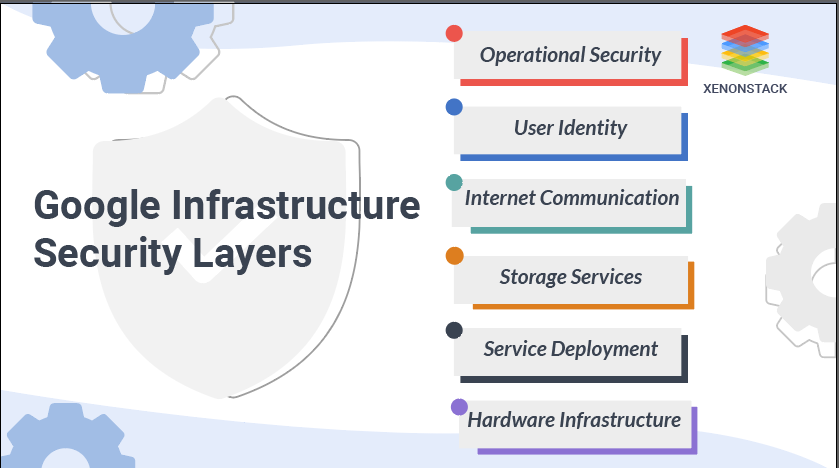 We will now discuss the Google Infrastructure Security Layers, which supports both the enterprise and the consumer. Enterprise services include GSuite and Google Cloud Platform.
We will now discuss the Google Infrastructure Security Layers, which supports both the enterprise and the consumer. Enterprise services include GSuite and Google Cloud Platform.
Secure Low-Level Infrastructure
We explain how we protect the lowest levels of our networks within this segment, from the physical premises to the purpose-built hardware within the data centers to the low-level software stack operating on any device.- Security of Physical Premises: Google uses multiple physical security layers to protect data center floors and use technologies like biometric identification, metal detection, cameras, vehicle barriers, and laser-based intrusion detection systems.
- Hardware Design and Provenance: A data center for Google consists of many server machines connected to a local network. Google custom-designs the server boards and the networking equipment.
- Secure Boot Stack and Machine Identity: Google server machines use various technologies like BIOS, bootloader, kernel, and base operating system image to ensure the correct software stack booting.
Secure Service Deployment
Let us describe how the hardware and software help to ensure that a service is deployed securely on our infrastructure.- Service Identity, Integrity, and Isolation: For inter-service communication, google uses cryptography authentication and authorization at the application layer. This provides robust and abstraction-level access control and granularity that administrators and services naturally understand.
- Inter-Service Access Management: The owner of a service can use the infrastructure's access management features to specify precisely which other services can communicate with it.
Secure Data Storage
Google implements secure data storage on the infrastructure.- Encryption at Rest: Google's infrastructure provides a wide range of storage services, including Bigtable and Spanner, as well as an essential management service.
- Deletion of Data: Deleting Google data most often starts with marking specific data as "deletion scheduled" rather than deleting the data.
Secure Internet Communication
Google isolates infrastructure from the Internet into a private IP space. Additional security such as the denial of service defenses (DoS) threats can be enforced more effectively by directly exposing a subset of machines specifically to external internet traffic.- Google Front End Service: If a service intends to be made available on the Internet, it can register itself with the Google Front End (GFE) infrastructure service.
- Denial of Service (DoS) Protection: Google's overwhelming scale of infrastructure allows Google to handle loads of DoS threats easily. Google has multi-tier, multi-layer DoS safeguards that further reduce the risk of any DoS effect on a GFE operation.
- User Authentication: The next layer of defense after DoS protection comes from google's central identity service. This service usually manifests to end users as the Google login page.
Operational Security
Last but not least, google operates the infrastructure securely from their employees' machines and credentials. Google defends against threats to the infrastructure from both insiders and external actors.- Safe Software Development: Google has a high emphasis on the secure environment for development; thus, it uses manual security reviews and in-depth design and implementation reviews for the riskiest features.
- Keeping Employee Devices and Credentials Safe: Google makes a considerable investment to protect their employees' equipment and credentials from compromise and monitor activities to identify potential compromises or illicit insider activity.
Application security describes the security measures at the application level that secures the data or the code from being stolen. Source: Application Security – Vulnerabilities Checklist
Securing Google Cloud Platform (GCP)
This section lets us determine how GCP, a public cloud infrastructure, benefits from underlying infrastructure security. To better understand the infrastructure and how it provides service-specific security improvements that we build on top of the infrastructure to GCP, let's take the example of Google Compute Engine. Compute Engine allows customers to run their virtual machines on the infrastructure of Google. The compute Engine consists of the management control plane and the virtual machines. Let's go-ahead to know more.- The Compute Engine control plane exposes its API via the GFE, leveraging infrastructure security features such as Denial of Service (DoS) protection and centrally managed support for SSL / TLS.
- End-user authentication to the Compute Engine control plane API is performed through Google's centralized identity service, providing security features such as hijacking detection. Authorization is done using the central IAM service in the cloud.
- The network traffic for the control plane, from the GFEs to the first service behind it and from other control plane networks, is properly authenticated and protected by the system. It passes from one data center to another.
- Compute Engine persistent disks are encrypted at-rest using keys protected by the central infrastructure's key management system.
- The isolation provided to the VMs is based on hardware virtualization using the open-source Kernel-based Virtual Machine Stack.
- Compute Engine's use of customer data obey the GCP use of customer data policy. Google does not access or use customer data, except when required to provide services to customers.
Google Security Checklist
- Require 2-Step Verification for admin accounts
- Enforce 2-Step Verification for users
- Don't use a super admin account for daily activities.
- Don't remain signed in to an idle super admin account.
- Set up admin email alerts
- Review the admin audit log
- Add recovery options to admin accounts.
- Enroll a spare security key
- Save the backup codes.
- Use unique passwords
- Prevent password reuse with password alert
- Regularly review activity reports and alerts.
- Know and approve which third-party can access GSuite core services
- Create a Whitelist of trusted apps
- Limit external calendar sharing
- Set up underlying Chrome OS and Chrome Browser policy
- Warn the users when chatting outside their domain
- Don't automatically share the contact information.
- Validate email with SPF, DKIM, and DMARC
- Disable the "Do not require sender authentication" setting for spam policies.
- Prevent automatic forwarding the incoming mail
- Enable comprehensive mail storage
- Enable additional attachment protection
- After that, enable enhanced pre-delivery message scanning.
- Enable additional attachment protection
- Limit group creation to admins
- Set up the private access to groups
- Enforce mobile password requirements (reduce risk if the device is lost)
- Encrypt data on mobile devices
- Enable mobile inactivity reports
- Disable location history
- Disable access to offline docs
- Do not permit users to establish add-ons for Docs from the add-on store.
Conclusion
Google Security Services are a must when it comes to catering Google Security for enterprises employing GCP and other Google Services. You may like to know about AWS Security Services with us now. Just keep in mind, 'We Never Stop at Success, We Go Ahead.'
Want to know about the services we offer in Google Cloud Security Service? Explore here our Google Cloud Security Service


