What is DevSecOps?
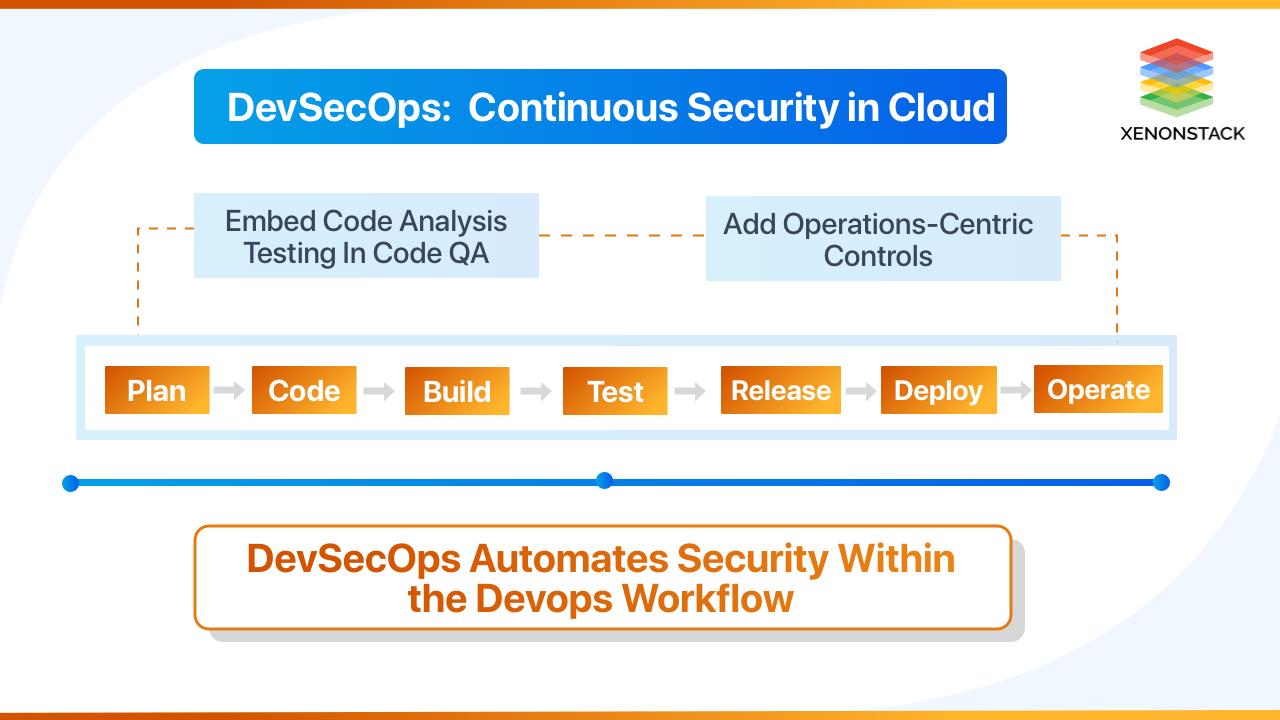
DevSecOps is all about introducing security in the earlier phase of the application or software development cycle and continuous integration, continuous delivery and continuous deployment pipelines (CI/CD), which helps to minimize vulnerabilities and meet IT and business objectives related to security and compliance. It mainly focuses on securing applications and automating security in the DevOps process. Good DevOps Security Tools and strategies are required to determine risk tolerance and conduct a risk/benefit analysis.
DevSecOps is a practice of implementing security at every step in the DevOps Lifecycle with DevSecOps Tools. According to the traditional method where penetration tests and vulnerability assessment were done after the build, DevSecOps is based on the concept of integrating security assessments and vulnerability tests at each point of the CI/CD pipeline. DevSecOps tools help in implementing security within the DevOps workflow.
DevSecOps is the answer to integrating various enterprise challenges into a coherent and effective approach to software delivery. A central tenet of DevSecOps Tools is that security is an integral and essential element of DevOps – the method by which enterprises innovate at speed and scale.
The DevSecOps Manifesto
- Leaning in over Always Saying, “No.”
- Data & Security Science over Fear, Uncertainty, and Doubt.
- Open Contribution & Collaboration over Security-Only Requirements.
- Relying on empowered development teams more than security specialists.
- Consumable Security Services with APIs over Mandated Security Controls & Paperwork.
- Business Driven Security Scores over Rubber Stamp Security.
- 24x7 Proactive Security Monitoring over Reacting after being Informed of an Incident.
- Shared Threat Intelligence over Keeping Info to ourselves.
- Compliance Operations over Clipboards & Checklists.
What's driving the DevSecOps Movement
As software continues to grow rapidly in IT, DevSecOps and DevSecOps Tools become the foundation of competitiveness in the modern marketplace. Every business must become an agile and innovative software delivery machine to survive. This leads all of us to the enterprise IT paradox: go faster and innovate. But always stay secure. Modern Applications are mostly “assembled.” Developers often use and download vulnerable open source components and application frameworks.
In the DevOps world, organizations are building applications faster than they have forgotten the Security aspect. Cloud platforms and continuous delivery life cycles often circumvent traditional security processes and checks.
Security Collaboration – it’s everyone's responsibility. Organizations must try to bring individuals of all abilities to a high level of proficiency in a short period of time.
DevSecOps, it’s going to enhance the purpose of DevOps. Taken From Article, A Quick Guide to DevSecOps Pipeline
Important DevSecOps Tools For DevOps Pipeline
- Automated Testing Tools
- Application Security Testing Tools
- Log Management Tools
- Monitoring Tools
- Alerting Tools
- Dashboard Tools
- Threat Modeling Tools
- Additional DevOps Security Tools
Automated Testing Tools
- [Code]AI
- Parasoft Tool Suite
[Code]AI
[Code]AI is a smart, automated, secure coding application that fixes security vulnerabilities in source code. Instead of listing a list of problems to resolve, it displays a list of solutions to review. Currently, it supports ten programming languages and can easily integrate with GitHub, GitLab, and other platforms.Parasoft Tool Suite
It is a set of tools that provides automated software testing and static analysis solution. It can perform functional testing, end-to-end testing, security testing, and load and performance testing.Application Security Testing Tools
- Checkmarx CxSAST
- Veracode
- BDD-Security
- Chef InSpec
- Fortify
Checkmarx CxSAST
The Checkmarx Software Exposure Platform includes the static analysis tool CxSAST. CxSAST seeks to locate security flaws in both proprietary and open-source code. The programme is compatible with more than 25 coding and scripting languages.
Veracode
It is a cloud-based software testing tool capable of performing static code analysis, dynamic code analysis, mobile application behavioral analysis, and software composition analysis. It helps to find security vulnerabilities, including detecting malicious codes and breaches caused due to the absence of some functionalities.
BDD-Security
A security testing framework that uses Behaviour Driven Development concepts to create self-verifying security specifications.
Chef InSpec
Chef InSpec is an open-source framework used for testing and auditing applications and infrastructure. It compares the state's actual state with the system's desired state expressed via the Chef InSpec code. It detects violations and generates a report based on the findings.
Fortify
It is a static code analysis tool. It has an integrated build tool that runs on the source code and converts the source code into an optimized security analysis format.
Log Management Tools
Log Management helps the organization and its environment function correctly as it helps to analyze and manage a large volume of logs generated in most organizations. Organizations need to discover and identify weak spots through either manual search or automated tools. Log Management tools help to serve this purpose. Many devices can be used for log management, monitoring, and alerting. Some of them are:
- Splunk
- SumoLogic
- Scalyr
- Nagios Fusion/Nagios Log Server
Splunk
It is a log management and analysis tool that searches, monitors, and analyzes machine-generated data through a web-based GUI interface in near real-time. Analyzing and processing machine data to extract required information is the most important because it holds the key to finding the solution to different problems by recognizing data patterns, producing metrics, and diagnosing problems, thereby providing insights on operations-related processes.
With Splunk's help, one can generate dashboards, visualizations, graphs, reports, and alerts by capturing, indexing, and correlating real-time data. It is beneficial and efficient and reduces the time taken to find the problem by quickly aggregating large volumes of logs. Through its advanced log searching and automated analysis capabilities, it can deploy Splunk. The organization also provides on-premises, as well as Splunk Cloud hosting options.
SumoLogic
It is a log management and analysis tool similar to Splunk used to collect, manage, and analyze log data. Moreover, it can generate dashboards, visualizations, graphs, reports, and alerts by capturing, indexing, and correlating data in real-time. SumoLogic also provides a web-based GUI interface. It can be availed as a cloud-based service or can be deployed on-premise. In addition to this, it can easily handle tremendous volumes of data and reduce the organization's time in performing the root cause analysis of the problem.Scalyr
It is also like Splunk and even somewhat looks like Splunk. Scalyr is a cloud-based solution. It includes tools for log management, dashboard building, visualization, and set alerts.Nagios Fusion/Nagios Log Server
Nagios Log Server is an open-source tool that provides monitoring, alerting, logging, and deployments.An organization's approach with DevSecOps is to make every person responsible for the software delivery implement their own security practices. Click to explore more, The Ultimate Guide to DevSecOps
Monitoring Tools
Monitoring tools help the organization have an eagle's eye view of their applications, deployments, infrastructure, and users, allowing them to quickly get the required information. These tools can have an auto-scaling feature, enabling the organization to scale the application with their changing needs.
- ExtraHop
- Datadog
- SignalFx
- Sqreen
- Tripwire
ExtraHop
ExtraHop aims to provide visibility into complex, high-performance infrastructure communications and help organizations determine congestions and hold-ups. It helps to widen the organizations' visibility by reconstructing failed data flows, thereby allowing the organization to find the primary cause of the problem and visualize the data flow across the network.Datadog
In a complex environment, Datadog, with its application performance management, monitors all aspects of the software infrastructure and helps the organization determine what's going on with different software components from the software internals' perspective. In datadog, an agent receives the data, which it incorporates with other collected data. So, datadog is more suitable for environments that do not generate data continuously.SignalFx
It is similar to Datadog in many ways, except that the collected data is sent to the SignalFx server for processing. The results are then displayed in a dashboard. SignalFx is more suitable for environments where data do have a specific format, i.e., environments with custom data collection. With SignalFx, tracking lost data becomes easy and can quickly identify incorrect custom data.Sqreen
An Application Security Management (ASM) framework unifies all the application security needs under one platform. Sqreen protects applications, increases visibility, and helps to secure code.Tripwire
It is a configuration control solution that helps proactively monitor configurations across data-center to ensure these configurations comply with internal and external policies. It scans, identifies, profiles, and validates all configuration changes on the network to ensure that these configurations remain in known and trusted states.Alerting Tools
Alerting Tools help organizations by providing and generating passive and active alerts. These are essential as whatever is observed by the Monitoring Tools and found suspicious should be conveyed to the appropriate personnel; else, having or not having Monitoring Tools will not matter if alerts are not generated. Alerting Tools also allow for teamwide communication and response. Some of the tools used are:
- VictorOps
- PagerDuty
- OpsGenie
- Alerta
- Contrast Assess
- Contrast Protect
- ElastAlert
- Immunio
VictorOps
It aims to provide incident visibility and cross-team communications (both broad and targeted) of issues and their status. It offers transparent and meaningful information to the users working outside their domain to work quickly and efficiently.PagerDuty
It provides a SaaS-based full incidence response and on-call management platform, including the artificial intelligence-based automated response. PagerDuty also includes the feature of creating on-the-fly updates. It can easily integrate with Slack, AWS, and many more applications.OpsGenie
It is a cost-effective alternative to PagerDuty and VictorOps. It is an incident management platform with alerting and on-call management and can easily integrate with applications such as Slack, AWS, Splunk, and many more.Alerta
Alerta tool accepts alerts from Syslog, Prometheus, Nagios, metadata, etc. With a warning, a single sign can be associated with multiple services. Alerta can receive an alert from any monitoring tool that can trigger a URL request and scripts anything that can also send signals using the command-line tool.Contrast Assess
This application security testing tool combines Static, Dynamic, and Interactive Application Security Testing (SAST, DAST, and IAST, respectively) to provide highly accurate and continuous information on your applications' security vulnerabilities.Contrast Protect
It is a runtime application protection (RASP), the solution that makes software self-protecting to identify and block application attacks from within a running application and defends itself from vulnerabilities and attacks.ElastAlert
It is a simple framework for alerting spikes, anomalies, or other interest patterns from data in Elasticsearch.Immunio
The Immunio tool helps to secure web applications by generating alerts when security events are triggered.Dashboard Tools
The two most important DevSecOps Dashboard Tools used in DevOps Pipeline are:Grafana
It is a multi-platform open-source analytics and interactive web-based visualization tool that deploys in combination with different time series databases such as Prometheus, Graphite, and InfluxDB. Grafana works with data stores and provides charts, graphs, and alerts.Kibana
It is an open-source data visualization dashboard. Kibana is a part of ELK Stack, which stands for ElasticSearch, Logstash, Kibana, and EFK Stack, which stands for ElasticSearch, Fluentd, and Kibana. It helps in providing visualization capabilities on top of the content indexed on an ElasticSearch cluster. It can be used on large volumes of data and can create bar graphs, lines, scatter plots, and pie charts.Threat Modeling Tools
The three most important tools used for DevOps Security in identifying, defining, and mitigating threats are as follows:- IriusRisk
- ThreatModeler
- OWASP Threat Dragon
IriusRisk
It is an open threat model platform that can create threat models and manage security risks throughout the entire software development life cycle using a template-based approach. IriusRisk applies security standards such as OWASP ASVS.ThreatModeler
It is an automated threat modeling solution that enhances the organization's security solution and helps the security team to make proactive security decisions. ThreatModeler helps in identifying, predicting, and defining threats. It features automation, integration, and collaboration to determine where the organization should apply most efforts.OWASP Threat Dragon
OWASP Threat Dragon is an open-source threat modeling tool from OWASP, which uses it to create threat model diagrams, possibly record threats, and decide mitigations. Its features include system diagramming and a rule engine to auto-generate threats and their comforts.Threat intelligence enables security teams to identify and mitigate security risks, respond quickly to security incidents, and improve overall security posture. . Click to explore about, Threat Intelligence for Security Monitoring and Incident Response
Additional DevOps Security Tools
- Redlock
- SD Elements
- WhiteSource
- WhiteHat Sentinel Application Security Platform
- Dome9 Arc
- Aqua Security
- SonarQube
- Signal Sciences
- Continuum Security
Redlock
It helps maintain compliance, govern security, and enable security operations across public cloud platforms. It supports Azure, AWS, and GCP platforms.SD Elements
These automate the security requirements based on technology in use, business needs, and compliance requirements across all software development stages. It helps identify critical areas of concern, eliminates vulnerabilities, and needs manual security testing.WhiteSource
It is an open-source security and compliance management solution based on the agile framework and can easily merge into the life cycle stages of software development. WhiteSource detects and remediates compliance issues by automating the entire process of open-source component selection, approval, and management.WhiteHat Sentinel Application Security Platform
It is a SaaS-based platform that delivers complete application security on a vast scale and with very high accuracy by combining automation, human intelligence, and artificial intelligence. It follows a distinctive approach and helps to quantify risk by finding the right balance between people, processes, and technology.Dome9 Arc
It is a SaaS platform that enables organizations to manage the security and compliance of their public cloud environments of any scale. It supports AWS, GCP, and Azure platforms.SonarQube
It helps to check codes for bugs and errors. This tool is mainly used for static code analysis and supports more than 27 different programming languages. It can be integrated easily into the CI/CD pipeline and provides the developers with security feedbacks about their codes. Incorporating into the CI/CD pipeline allows the agile software development environment to run security checks for every commit or pull request (PR).Signal Sciences
It is a next-gen Web Application Firewall (WAF) and Runtime Application Self-Protection (RASP) tool that helps the DevOps team ensure web application APIs protection from malicious activities and monitoring performance. Based on the SaaS model, it can integrate with other applications using an agent model. It supports AWS, GCP, IBM Cloud, and other cloud platforms. Signal Sciences agent works under Kubernetes, and the cloud engine automatically updates the signatures and rules related to the latest threats.Continuum Security
It is a set of integrated tools that help manage and test products' security. IriusRisk and BDD Security are the two primary modules that are present in Continuum Security. IriusRisk enables R&D teams to create a threat model, map it to security requirements, and manage the security risks throughout the Software development Life Cycle.Seven Rules for a DevSecOps Practitioner
Security starts with engineering; try to understand that developers are engineers, whereas hackers are reverse engineers.- Encourage good security hygiene in engineering.
- Continuous assessments and compliance checks.
- Real-time threat alerting across apps and services.
- Enable developers to drive iterative security changes.
1. Improving Your Security DNA
- Code Analysis
- Change Management
- Compliance Monitoring
- Threat Investigation
- Vulnerability Management
- Security Training
2. Code Analysis
- Secure the CI/CD pipeline.
- Release in small and frequent batches.
- Embed code analysis into Q/A.
- Use tools to detect that private keys or API s information is not pushed on the Version Control.
3. Change Management
- Empower teams to improve security practices and make changes.
- Quick review and approval process.
- Changes must leave the audit trail.
- Meet compliance requirements.
4. Compliance Monitoring
- Enforce operational and security hygiene.
- Establish strict password policies.
- Audit everything from code pushes, pipelines, and compliances.
- Monitor systems for bad behavior.
5. Threat Investigations
- Monitor app and services to detect and alert on threats.
- Instrument services to identify comprises.
- Built-in real-time alerting and controls.
- Develop Ansible playbooks and response scenarios for IT and Security.
6. Vulnerability Checks
- Conduct vulnerability scans and practices.
- Conduct periodic scans of the product build.
- Code reviews and penetration tests.
- Establish remediation SLAs.
7. Security Training
- Transform the team into security ninjas.
- Participate in industry conferences.
- Invest in security certifications.
- Educate employees on security risks.
- Prepare teams for incident response.
DevSecOps is injecting security into the DevOps lifecycle. Click to explore about, A Guide to DevSecOps Security Checklist
Integrate Security into Continuous Delivery workflows
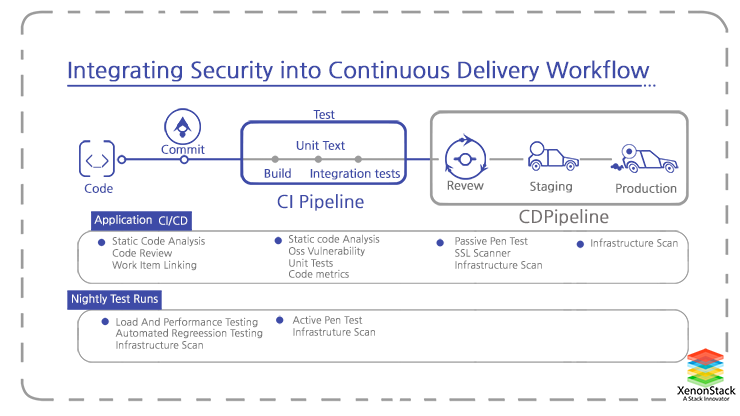
Let's see how and where to add security checks into a Continuous Delivery workflow.
1. Pre-commit
-
- Lightweight, iterative threat modeling, and risk assessments.
- Static analysis (SAST) checking in the engineer’s IDE.
- Peer code reviews (for defensive coding and security vulnerabilities).
2. Commit Stage
- Compile and build checks, ensuring that these steps are clean and no errors or warnings.
- Try to identify risk in third-party components.
- Generating Alerts on the high-risk code.
- Automation of unit testing of security functions, with full coverage of code analysis.
3. Acceptance stage
- Secure, automated configuration management and provisioning using tools such as Ansible and Chef.
- Targeted dynamic scanning (DAST).
- Automated functional and integration testing of security features.
- Deep static analysis scanning.
- Manual Penetration Testing using web exploitation frameworks such as Metasploit.
4. Production deployment and post-deployment
- Automated deployment and release orchestration.
- Automated runtime asserts and compliance checks.
- Production monitoring/feedback.
- Runtime defense.
- Bug bounties.
- Learning from failure
- Depending on the risk and uncertainty profile of your organization and infrastructure, you shall need to implement these practices and controls.
Architecting Container Infrastructure for Continuous Security and Compliance
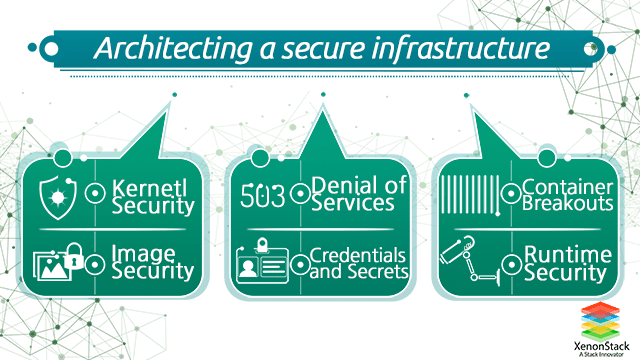
As organizations benefit from agility, scalability, and even migrating to containers and microservices, Security and compliance parameters are often overlooked—some of the most critical security listings for container infrastructure.
- Kernel Security
- Denial Of Service
- Image Security
- Credentials and Secrets
- Runtime Security
1. Kernel Security
When it comes to containers and microservices, all rely on a single kernel of the host machine. Most of the intrusions can be stopped if proper kernel security is implemented. This is really efficient for multiple reasons you probably know already, but from the point of view of security, it can be seen as a risk that needs to be mitigated
2. Docker Host and Kernel Security
If an attacker compromises your host system, then container isolation and security safeguards won’t make much difference. Besides, containers run on top of the host kernel by design.
- Make sure your host and Docker engine configuration are secure. Watry using the Docker bench audit tool to check configuration best practices.
- Keep your base system reasonably updated, subscribe to security news feeds for the os and any software installed for 3rd party repositories, like the container orchestration platforms.
- Using minimal, container-centric host systems like CoreOS, Redhat Atomic, RancherOS, etc.
- You can use Mandatory Access Control to prevent undesired operations both on the host and on the containers at the kernel level using tools like Seccomp or Selinux.
- Ensure you have the removed lethal kernel modules; packages such as xinetd and telnet can be lethal, and privileges and access should be ensured accordingly.
Security vulnerabilities can exist in OSS (Open source software) libraries that we import as much as we write. Tons of developers do programming every day, and manual code reviews don't scale. Here is the real power of DevSecOps lies. Click to explore about, Relationship of DevSecOps with CI/CD Pipeline
3. Distributed Denial Of Service
Distributed denial of service DDOS attacks are some of the most pervasive and difficult attacks to prevent. These kinds of attacks use many distributed endpoints and systems to flood a web domain, application, or service with an excess number of service requests or application calls.
Running penetration tests on software early in development is one way to thwart holes that enable L7 DDoS attacks.
The failed test requires a response. One such response is to build the software when the software fails the test automatically. If development can't move forward without fixing the security holes, the security holes will be fixed.
Developers should not have to do a lot of digging to uncover these methods. Use resources such as the Open Web Application Security Project ( OWASP ) clearly set these approaches apart and label each of them independently.
4. Image Security
Many images are available on different repositories on the internet doing all kinds of useful stuff. Still, if you pull images without trust, authenticity, or vulnerability scanning, you are running arbitrary software on your machine.
Certain parameters must be followed before using that docker image:-
- Where did the image come from?
- Do you trust the image creator? Which kind of security policy are they using?
- How do you know nobody has been tampering with the image?
Best Practices to follow
- Do not run unverified software and/or from sources you don’t explicitly trust.
- Deploy a container-centric trust server using some of the Docker registry servers in our Docker Security Tools list.
- Enforce mandatory signature verification for any image that is going to be pulled or running on your system.
5. Credentials and Secrets
Your software needs sensitive information to run, such as user password hashes, server-side certificates, and encryption keys. The microservices deployed on containers are plenty and may constantly be created and destroyed.
You need an automatic and secure process to share this sensitive info.
Best Practices to follow
- Do not use environment variables for secrets; this is a widespread yet very insecure practice.
- Do not embed any secrets in the container image. Like “The private key and the certificate were mistakenly left inside the container image.”
- Deploy a Docker credentials management software if your deployments get complex enough, Do not attempt to create your own ‘secrets storage’ unless you know really well what you are doing.
6. Docker runtime security monitoring
As we build Docker container images, we need to know exactly what goes into each container layer. We also must ensure that containers installed by third-party vendors do not download and run anything at runtime.
A Holistic Approach
Towards Automation and Continuous Security using DevSecOps Tools
DevSecOps is all about implementing security at every step in the DevOps Lifecycle. it is an approach to secure an application and infrastructure using DevSecOps Tools based on DevOps, making sure the application is less vulnerable and ready for user use. All things automated, and security checks started from the beginning of the application’s pipelines.
With DevSecOps Tools, it is easier to identify and mitigate vulnerabilities and deliver more secure products. It allows the organization to take a proactive approach toward security. DevSecOps Tools enables the development, safety, and operations teams to work closely and deliver better results within the same frame but with relatively fewer efforts. It also allows the organization to monitor the products for new security threats as DevSecOps tools can be easily merged into the CI/CD pipeline.